Tailscale
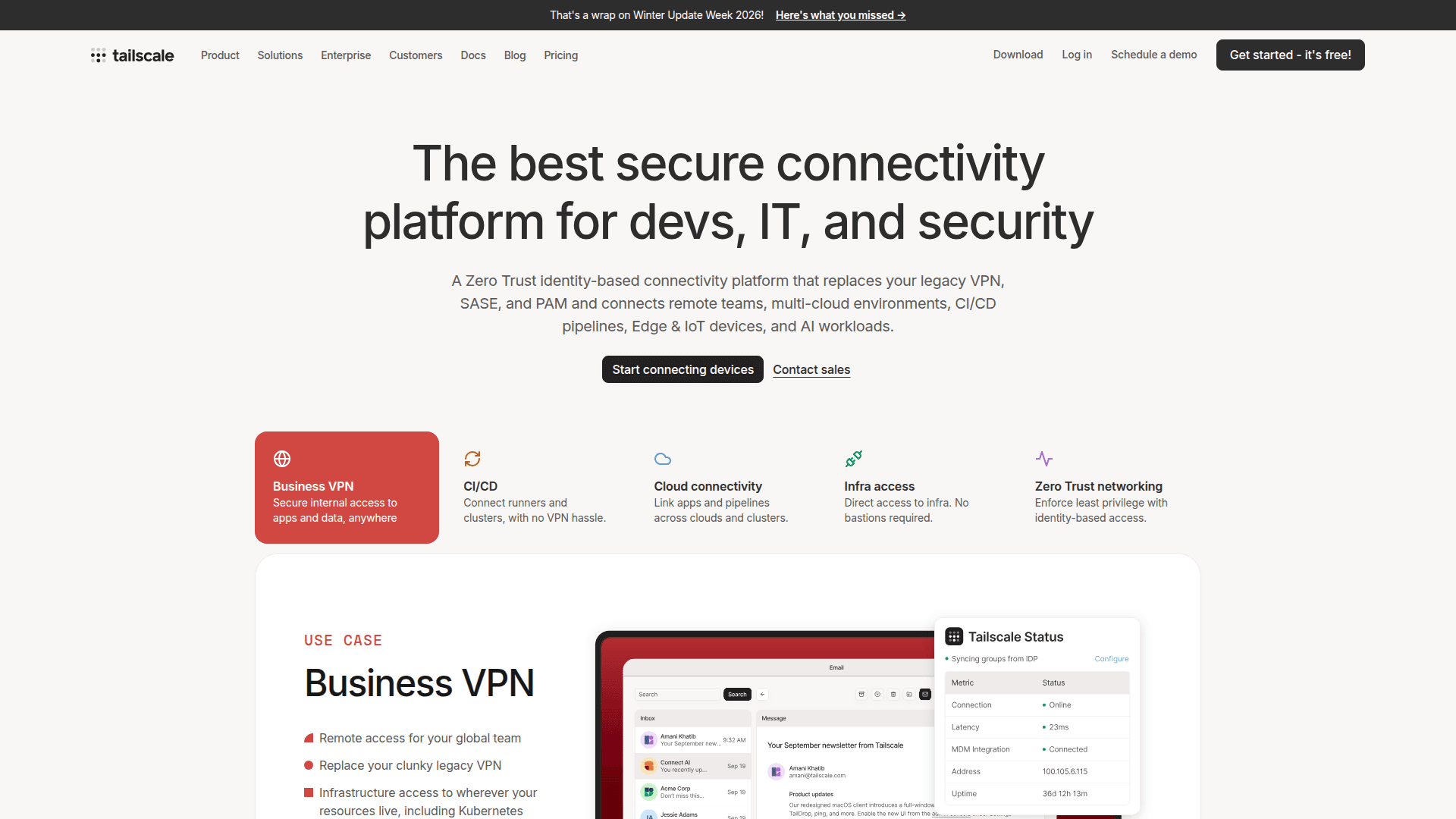
A Zero Trust identity-based connectivity platform that replaces legacy VPNs and connects remote teams, multi-cloud environments, CI/CD pipelines, Edge & IoT devices, and AI workloads.
At a Glance
About Tailscale
Tailscale is a Zero Trust identity-based connectivity platform built on WireGuard® that replaces legacy VPNs, SASE, and PAM solutions. It creates a secure mesh overlay network (tailnet) that connects remote teams, multi-cloud environments, CI/CD pipelines, Edge & IoT devices, and AI workloads with minimal configuration. Tailscale deploys in minutes, works across all major operating systems and cloud providers, and enforces least-privilege access using identity-aware access control lists (ACLs).
- Zero Trust networking — Enforce identity-based access controls using your existing identity provider (Okta, Entra ID, custom OIDC) with SSO, MFA, and SCIM provisioning.
- WireGuard® encryption — All traffic is end-to-end encrypted using WireGuard®, establishing direct peer-to-peer connections between nodes to minimize latency.
- MagicDNS — Automatically assigns human-readable DNS names to devices and services on your tailnet, eliminating the need to manage IP addresses manually.
- Subnet routers & exit nodes — Extend your tailnet to existing subnets, VPCs, and corporate LANs without installing Tailscale on every device, and route internet traffic through designated exit nodes.
- Tailscale SSH — Authenticate and encrypt SSH connections using Tailscale identity instead of managing SSH keys, certificates, or bastions.
- Tailscale Funnel — Expose services on your tailnet to the public internet without opening firewall ports, available on Premium and above.
- Kubernetes Operator — Provide full ingress and egress connectivity from Kubernetes clusters to non-Kubernetes resources and enable cross-cluster peering.
- Access Control Lists (ACLs) — Define granular network policies as code, manage them via GitOps workflows, and test them before deployment.
- Device posture management — Collect device attributes and enforce connectivity rules based on security posture, with integrations for third-party posture tools.
- Monitoring & compliance — Stream configuration audit logs and network flow logs to any SIEM or observability tool; record Tailscale SSH and Kubernetes Operator sessions.
- Infrastructure as Code — Manage your tailnet configuration using Terraform or Pulumi providers.
- Cross-platform support — Available on Linux, macOS, Windows, iOS, Android, and deployable via CLI, API, and over 100 integrations.
Community Discussions
Be the first to start a conversation about Tailscale
Share your experience with Tailscale, ask questions, or help others learn from your insights.
Pricing
Personal
For individuals who want to securely connect personal devices, for free.
- Limited to 3 users
- 100 devices
- Access nearly all of Tailscale's features
- Use Tailscale for free, indefinitely
Personal Plus
For individuals who want to securely connect personal devices with friends and family.
- Limited to 6 users
- 100 devices
- Access nearly all of Tailscale's features
- Share Tailscale with family and friends
Starter
For small teams seeking an easy-to-use and quick-to-deploy secure network access solution.
- 100 devices + 10 per user
- Multiple OS/platform/cloud compatibility
- Split tunnelling
- MagicDNS
- Network-level access policies (ACLs - limited functionality)
- Kubernetes networking through Tailscale Kubernetes Operator
- First two weeks free
Premium
For growing teams seeking advanced service/resource-level networking and identity-aware access controls.
- 100 devices + 20 per user
- Automatic key management through Tailscale SSH
- Advanced service-level networking through Tailscale Funnel
- Identity-aware access policies (ACLs - full functionality)
- MDM policies
- Configuration audit and network flow logging
- Priority support
- First two weeks free
Enterprise
For organizations seeking advanced user and posture management, robust compliance, and dedicated support.
- Custom device limits
- Integrations for user/group provisioning
- Endpoint management through Tailnet Lock
- Advanced posture management
- Tailscale SSH and Kubernetes Operator recording and log streaming
- Dedicated support
- Options to pay by invoice and/or annual billing
Capabilities
Key Features
- Zero Trust identity-based access control
- WireGuard® end-to-end encryption
- Peer-to-peer mesh networking
- MagicDNS for human-readable device names
- Subnet routers and exit nodes
- Tailscale SSH (keyless SSH)
- Tailscale Funnel (public internet exposure)
- Kubernetes Operator
- ACLs as code with GitOps support
- SSO with any OIDC identity provider
- SCIM user and group provisioning (Okta, Entra ID)
- Device posture management
- Configuration audit logging
- Network flow logging
- SSH and Kubernetes session recording
- Log streaming to SIEM
- Tailnet Lock
- MDM policy support
- Terraform and Pulumi providers
- App connectors for SaaS access
- HA failover for subnet routers
- Regional routing
- On-demand and just-in-time access
- Webhooks for event subscriptions