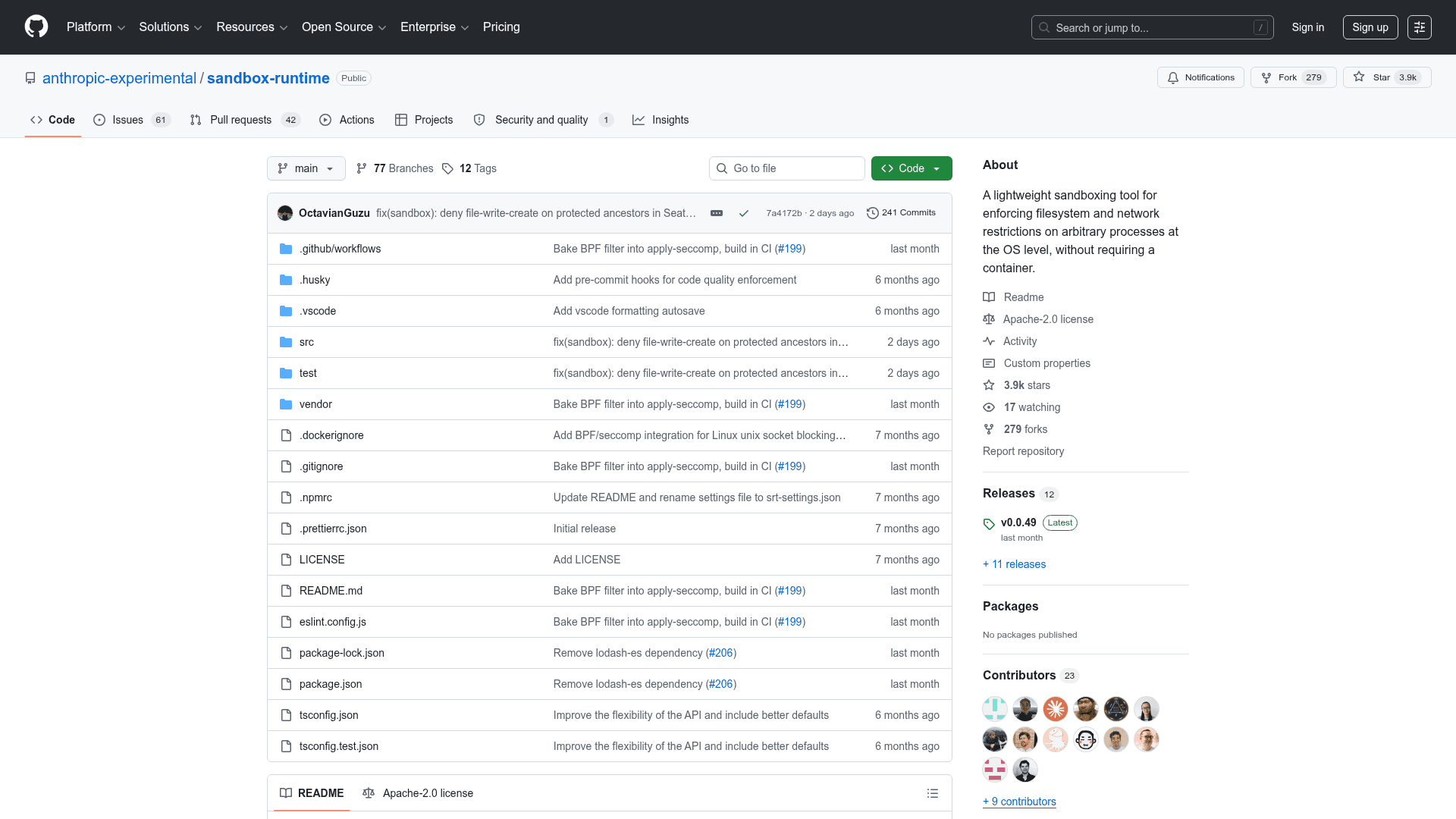
Anthropic Sandbox Runtime
A lightweight CLI and library for enforcing filesystem and network restrictions on arbitrary processes at the OS level using native sandboxing primitives, without requiring a container.
At a Glance
About Anthropic Sandbox Runtime
Anthropic Sandbox Runtime (srt) is an open-source security tool that wraps arbitrary processes with OS-level filesystem and network restrictions, using sandbox-exec on macOS and bubblewrap on Linux. Developed as part of Claude Code to enable safer AI agents, it follows a secure-by-default philosophy where processes start with minimal access and permissions are explicitly granted. It can be used as both a CLI tool and a TypeScript/Node.js library, making it suitable for sandboxing MCP servers, AI agents, bash commands, and any arbitrary process.
- Network restrictions: Uses an allow-only pattern — all network access is denied by default; explicitly allow domains (with wildcard support) via
allowedDomains. HTTP/HTTPS traffic is routed through a built-in HTTP proxy, and other TCP traffic through a SOCKS5 proxy. - Filesystem restrictions: Read access uses a deny-then-allow pattern (allowed everywhere by default, deny broad regions and re-allow specific paths); write access uses an allow-only pattern (denied everywhere by default, must explicitly allow paths).
- Unix socket restrictions: Blocks Unix domain socket creation at the syscall level on Linux via seccomp BPF filters; on macOS, uses Seatbelt allowlists.
- MCP server sandboxing: Drop-in wrapper for Model Context Protocol servers in
.mcp.jsonto restrict their filesystem and network capabilities. - Violation monitoring: On macOS, taps into the system sandbox violation log store for real-time alerts; on Linux, violations can be traced via
strace. - Mandatory deny paths: Automatically blocks writes to sensitive files (
.bashrc,.zshrc,.gitconfig,.mcp.json,.git/hooks/, etc.) regardless ofallowWriteconfiguration. - CLI usage: Install globally via
npm install -g @anthropic-ai/sandbox-runtimeand runsrt <command>to wrap any command with sandbox restrictions. - Library usage: Import
SandboxManagerfrom@anthropic-ai/sandbox-runtimeto programmatically initialize sandboxes and wrap commands in TypeScript/Node.js applications. - Configuration: Controlled via
~/.srt-settings.jsonor a custom path specified with--settings; supports glob patterns on macOS and literal paths on Linux. - Platform support: macOS (no extra dependencies) and Linux (requires
bubblewrap,socat,ripgrep); Windows not yet supported.
Community Discussions
Be the first to start a conversation about Anthropic Sandbox Runtime
Share your experience with Anthropic Sandbox Runtime, ask questions, or help others learn from your insights.
Pricing
Open Source
Free and open-source under the Apache License 2.0. Install via npm and use without restrictions.
- Full CLI and library access
- Network filtering (HTTP proxy + SOCKS5 proxy)
- Filesystem read/write restrictions
- Unix socket blocking
- MCP server sandboxing
Capabilities
Key Features
- OS-level process sandboxing without containers
- Network allow-only filtering via HTTP and SOCKS5 proxies
- Filesystem read (deny-then-allow) and write (allow-only) restrictions
- Unix socket blocking via seccomp BPF on Linux
- MCP server sandboxing support
- Violation monitoring and logging
- Mandatory deny paths for sensitive files
- CLI and TypeScript library interfaces
- Wildcard domain support for network rules
- Glob pattern support for filesystem rules on macOS
- Configurable via JSON settings file
- Bring-your-own-proxy support for advanced filtering
- Secure-by-default philosophy
- macOS sandbox-exec (Seatbelt) integration
- Linux bubblewrap containerization